Responsible Disclosure Policy

- Terms and Conditions
- Security Policy
- Privacy Policy
- Cookie Policy
- GDPR Policy
- Anti-corruption and Anti-bribery
- Modern Slavery Policy
- Equality and Diversity Policy
- Customer Fair Treatment Policy
- Responsible Disclosure Policy
- Third Party List
- Accessibility Statement
- AI Bias and Fairness Policy
- Data Processing Addendum (DPA)
At Learn Amp, we take security seriously and respond swiftly to fix verifiable security issues. If you think you have found a potential security issue within our platform then please report this responsibly following the guidelines provided on this page.
If you are the first to report a verifiable security issue, we’ll thank you with a place on our Hall of Fame page as well as a reward based on severity of the issue found.
We encourage anyone to report security issues to disclosure@learnamp.com.
Contents
- Who can participate?
- Which domains are in scope?
- How to format reports
- Guidelines for testing and reporting
- What bugs are eligible?
- What bugs are not eligible?
- Rewards
Who can participate?
Anyone who doesn't work for Learn Amp or partners of Learn Amp who reports a unique security issue in scope and does not disclose it to a third party before we have patched and updated the issue.
Which domains are in scope?
In Scope:
- learnamptesting.learnamp.com
- api.learnamp.com
Out of Scope:
- learnamp.com (marketing website)
- blog.learnamp.com
- support.learnamp.com
How to format reports
Please include a detailed report of the security vulnerability found including:
- Title
- Bug Type
- The Domain the vulnerability was found on
- Severity (we assign severity using CVSS scoring v3)
- URL
- Detailed steps to recreate including screenshots and/or videos
- Potential impact
- Mitigation
Guidelines for testing and reporting
- You must not attempt to access anyone’s data, personal or otherwise. This includes, but is not limited to, customer data, passwords and other credentials. If you gain access to anyone’s data, personal or otherwise, you must stop testing and contact us immediately by emailing disclosure@learnamp.com. You must not save, store or transmit this information.
- You must disclose any issues to us directly and responsibly.
- You must allow us time to verify, investigate and resolve the issues reported.
- Do not use automated scanners or tools which can negatively impact our data or services.
What bugs are eligible?
Any typical web security bugs such as:
- Cross-site Scripting
- Open redirect
- Cross-site request forgery
- FIle Inclusion
- Authentication bypass
- Remote Code Execution
- SQL Injection
What bugs are not eligible?
Disruptive bugs or bugs with no/low impact or likelihood such as:
- Missing Cookie flags on non-session cookies or 3rd party cookies
- Social engineering
- Denial of service
- Weak TLS ciphers
- Email spoofing, SPF, DMARC & DKIM
- Brute force attacks
- Password policy improvements
- Hardening tips (such as missing CSP header or SRI attribute)
Rewards
We offer rewards based on the severity of a vulnerability, as well as a place on our Hall of Fame. Rewards will be awarded to the first person to report the vulnerability. Rewards will not be offered to duplicate reports of a vulnerability which has already been reported. Learn Amp uses the severity levels of:
| Severity | Reward |
|---|---|
| P1 Critical | $1500 and a place on the Hall of Fame |
| P2 High | $750 and a place on the Hall of Fame |
| P3 Medium | Place on the Hall of Fame |
| P4 Low | Place on the Hall of Fame |
Please note, however, that reward decisions are up to the discretion of Learn Amp.
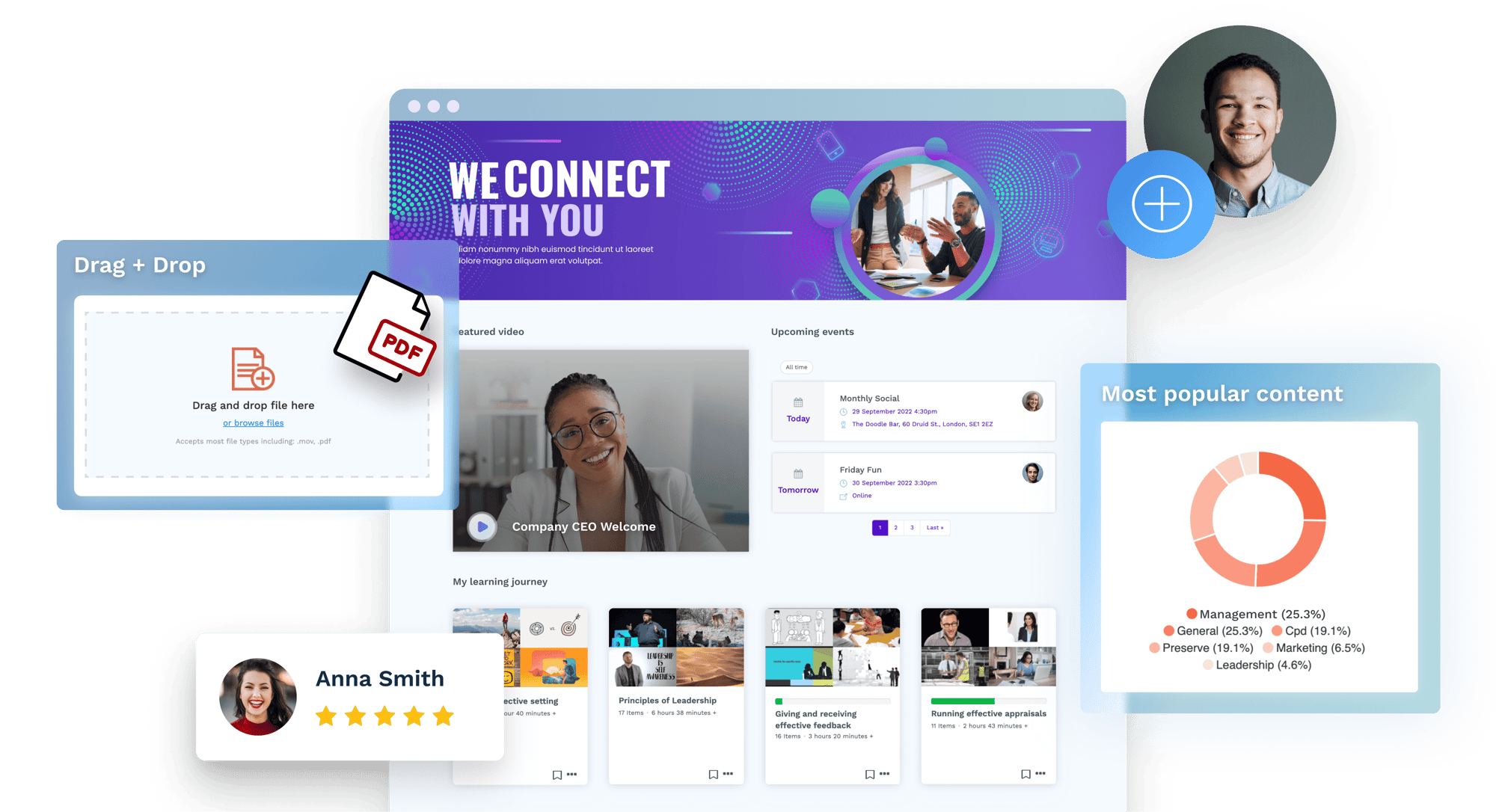
Try Learn Amp yourself
Take the first step to a new learning system your employees will love.