Security Policy
Rise To Ltd (Trading as Learn Amp)

- Terms and Conditions
- Security Policy
- Privacy Policy
- Cookie Policy
- GDPR Policy
- Anti-corruption and Anti-bribery
- Modern Slavery Policy
- Equality and Diversity Policy
- Customer Fair Treatment Policy
- Responsible Disclosure Policy
- Third Party List
- Accessibility Statement
- AI Bias and Fairness Policy
- Data Processing Addendum (DPA)
Security measures for Learn Amp platform and services
This document describes technical and organizational security measures and controls implemented by Learn Amp to protect Personal Data and ensure the ongoing confidentiality, integrity and availability of Learn Amp Services.
Learn Amp may change these measures from time to time. This may mean that individual measures are replaced by new measures that serve the same purpose or deal with the same risks without materially diminishing the security level. In the unlikely event that Learn Amp does materially reduce its security, Learn Amp shall formally notify Customers.
Definitions
Within this document, the following definitions apply:
- “Customer” means any purchaser of Learn Amp services
- "Learn Amp platform" and "Learn Amp services" means the Software-As-A-Service provided by Learn Amp to the Customer for the creation, aggregation, delivery, monitoring and reporting of Learning and associated services.
- “Personal Data” means any information provided or submitted by the Customer or Participants in the creation, participation or reporting of learning or during sales activities
- “Personnel” means Learn Amp employees and authorised individual contractors.
- “Learn Amp” means Rise To Limited. When Learn Amp Personnel or systems are referred to, this includes those of our affiliate companies.
- “Strong Encryption” means the use of industry standard encryption measures compliant with FIPS 140-2.
This document is a high-level overview of Learn Amp’s technical and organisational measures.
1. Organisation of Information Security
Objective
All Learn Amp are responsible for implementing security measures, supported by business leadership and Learn Amp ensures that its Personnel are competent in information security.
Measures include:
- Learn Amp has a comprehensive set of information security policies, approved by senior management and disseminated to all Personnel.
- Learn Amp security policies are reviewed at least annually and updated when needed.
- All Learn Amp Personnel have signed legally reviewed confidentiality agreements that apply during and post-engagement.
- Failure of Personnel to follow information security policies can be treated as a disciplinary matter and lead to sanctions, including dismissal.
- All Learn Amp Personnel are given training in information security and must take and pass a test on information security at least annually.
- Information security is a basic design and architectural principle for the Learn Amp platform
- Learn Amp is committed to continual improvement of its security.
- Continuous, around-the-clock SIEM Monitoring is implemented to oversee system access, data access and data transmission activities every day throughout the year.
2. Physical Access
Objective
Physical access to Personal Data is protected.
Measures include:
- Learn Amp run their platform from an ISO 27001 certified, professional, third-party production data centre with a defined and protected physical perimeter, strong physical controls including access control mechanisms, controlled delivery and loading areas, surveillance and 24x7x365 guards. Only authorized representatives have access to the data centre premises (double authentication no fewer than 3 times).
- Climate control is required to maintain a constant operating temperature for servers and other hardware, which prevents overheating and reduces the possibility of service outages. Data centres are conditioned to maintain atmospheric conditions at optimal levels. Monitoring systems and data centre personnel ensure temperature and humidity are at the appropriate levels.
- Automatic fire detection and suppression equipment has been installed to reduce risk. The fire detection system utilizes smoke detection sensors in all data centre environments, mechanical and electrical infrastructure spaces, chiller rooms and generator equipment rooms. These areas are protected by either wet-pipe, double-interlocked pre-action, or gaseous sprinkler systems
- The data centre electrical power systems are designed to be fully redundant and maintainable without impact to operations, 24 hours a day, and seven days a week. Uninterruptible Power Supply (UPS) units provide back-up power in the event of an electrical failure for critical and essential loads in the facility. Data centres use generators to provide backup power for the entire facility.
- When Personal Data is transferred electronically by Learn Amp, appropriate physical security is maintained and the data is Strongly Encrypted at all times.
3. System Access
Objective
Learn Amp data processing systems are used only by approved, authenticated users.
Measures include:
- Access to Learn Amps internal systems is granted only to Learn Amps Personnel and/or to permitted employees of Learn Amp subcontractors and access is strictly limited as required for those persons to fulfil their function.
- All users access Learn Amp systems with a unique identifier (user ID)
- Learn Amp has established a password policy that prohibits the sharing of passwords and requires passwords to be changed on a regular basis and default passwords to be altered. All passwords must fulfil defined minimum requirements and are stored in encrypted form. Each computer has a password-protected screensaver
- A second factor of authentication is required for access to online systems containing Personal Data
- Learn Amp has a thorough procedure to deactivate users and their access when a user leaves the company or a function.
- Continuous, around-the-clock SIEM Monitoring is implemented to oversee system access activities every day throughout the year.
4. Data Access
Objective
Persons entitled to use data processing systems gain access only to the Personal Data that they are authorised to access.
Measures include:
- Learn Amp restricts Personnel access to files and programs on a "need-to-know” basis
- Personnel training covers access rights to and general guidelines on definition and use of Personal Data.
- Where appropriate and practical, Learn Amp employs data minimisation and pseudonymisation to reduce the likelihood of inappropriate access to Personal Data.
- Continuous, around-the-clock SIEM Monitoring is implemented to oversee data access activities every day throughout the year.
5. Data Transmission
Objective
Prevent Personal Data from being read, copied, altered or deleted by unauthorized parties during transfer.
Measures include:
- Customer access to the Learn Amp is protected by TLS 1.2 or higher.
- Learn Amp uses Strong Encryption for all other transmission of Personal Data outside the production data centre.
- Any Personal Data stored outside the production data centre is protected by Strong Encryption at rest
- Continuous, around-the-clock SIEM Monitoring is implemented to oversee data transmission activity every day throughout the year.
The Customer is responsible for the security of Personal Data once it has been transmitted from Learn Amp to the Customer including when downloaded or accessed by Customer users.
6. Confidentiality and Integrity
Objective
Personal Data remains confidential throughout processing and remains intact, complete and current during processing activities.
Measures include:
Learn Amp has a defence in depth approach to ensuring confidentiality and integrity and many of the measures in other sections of this document safeguard confidentiality and integrity. Some other measures that contribute include:
- Learn Amp trains and tests its software engineers and quality assurance Personnel in application security practices and secure coding practices.
- Learn Amp has a central, secured repository of product source code, which is accessible only to authorized Personnel.
- Learn Amp has a formal product development security policy and uses a Secure Development Lifecycle (SDLC) that includes a wide range of security testing and a flaw reporting and management procedure.
- Security testing includes code review and employing static code analysis tools on a periodic basis to identify flaws.
- All changes to software on the Learn Amp are via a controlled, approved release mechanism within a formal change control program that tracks, documents, tests, and approves change requests prior to implementation.
- All encryption and other cryptographic functionality used within Learn Amp (except for interfaces to third parties) that has a security purpose uses industry standard encryption and cryptographic measures compliant with the standards promulgated with FIPS 140-2.
7. Availability
Objective
Personal Data is protected from accidental destruction or loss, and there is timely access, restoration or availability to Personal Data in the event of an incident.
Measures include:
- Learn Amp uses a high level of redundancy at the production data centre so that an availability failure of a single system or component is unlikely to impact general availability.
- The production data centre has multiple power supplies, generators on-site and with battery back-up to safeguard power availability to the data centre.
- The production data centre has multiple access points to the Internet to safeguard connectivity.
- The production data centre is monitored 24x7x365 for power, network, environmental and technical issues.
- Learn Amp uses commercially reasonable efforts to create frequent, encrypted back-up copies of Personal Data and these are stored in a geographically separate location to the data centre. Learn Amps storage vendor for backups is ISO 27001 certified.
- Learn Amp has a system in place to ensure that any failures of backup to operate correctly are flagged and dealt with.
- Learn Amp performs restore tests from those backups at least quarterly.
- Learn Amp has a business continuity plan in place which is regularly updated.
- Learn Amp tests elements of its business continuity plan regularly and learns from the results of such tests.
8. Job Control
Objective
Personal Data processed on a Customer’s behalf is processed solely in accordance with the relevant agreement and related instructions of the Customer including in the use of sub-processors.
Measures include:
- Learn Amp acts as data processor with respect to Personal Data and stores and processes Personal Data in order to operate Learn Amp platform under the instructions of Customer.
- Learn Amp does not access Customer Personal Data, except to provide services to the Customer which Learn Amp is obligated to perform in support of the Customer experience including for general operation and monitoring of the Learn Amp platform, troubleshooting and maintenance purposes, for security reasons, as required by law, or on request by Customer.
9. Data Separation
Objective
Personal Data collected for different purposes is processed separately.
Measures
- Learn Amp uses a multi-tenant architecture to achieve logical separation of Personal Data originating from multiple Customers.
- In each step of the processing, Personal Data received from different Customers can be identified so data is always physically or logically separated
- Customers have access only to their own Personal Data
- Audit rights given to Customers always exclude the right or ability to look at the data of other Learn Amp Customers.
10. Incident Management
Objective
In the event of any security breach of Personal Data, the effect of the breach is minimized and the Customer is promptly informed
Measures
- Learn Amp maintains an up-to-date incident response plan that includes responsibilities, how information security events are assessed and classified as incidents and response plans and procedures.
- Learn Amp logs administrator and user activities at the production data centre to provide evidence in the event of an incident.
- The clocks of all systems at the production data centre are synchronized to a single reference time source to aid investigation in the event of an incident.
- Learn Amp regularly tests its incident response plan with “table-top” exercises and learns from tests and potential incidents to improve the plan.
- In the event of a security breach, Learn Amp will notify Customers without undue delay after becoming aware of the security breach.
11. Compliance
Objective
Learn Amp tests, assesses and evaluates the effectiveness of these technical and organisational measures.
Measures
- Learn Amp conducts regular internal and external audits of its security
- Learn Amp has a formal policy for managing suppliers who have access to Personal Data and this includes criteria for reviewing and approving suppliers and procedures for monitoring and reviewing their performance.
- Learn Amp takes reasonable steps to ensure that Personnel are aware of and comply with the technical and organizational measures set forth in this document.
- Learn Amp internally conducts at least quarterly application vulnerability scan penetration tests on the Learn Amp platform.
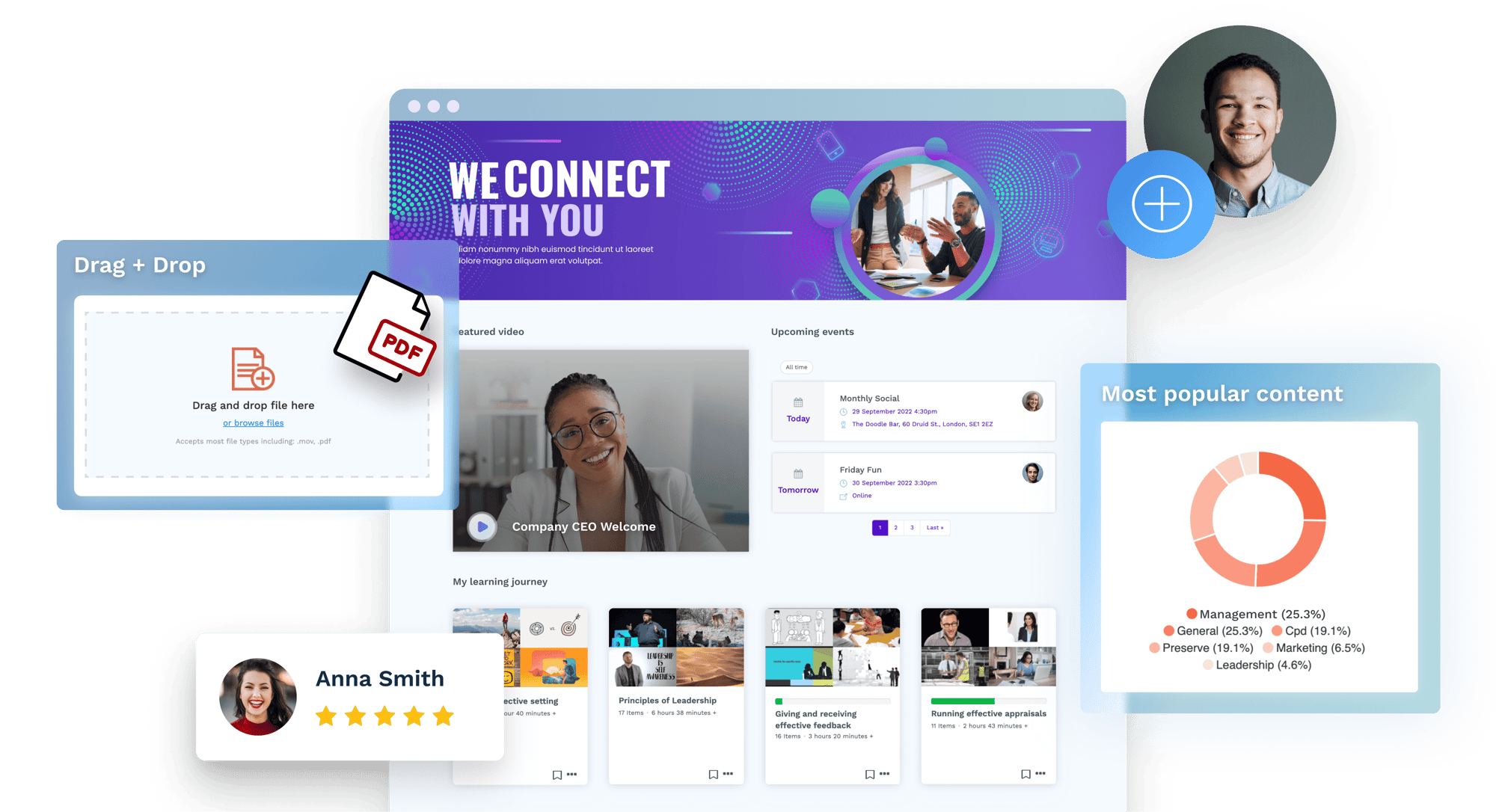
Try Learn Amp yourself
Take the first step to a new learning system your employees will love.